Recently, I encountered an intriguing Capture The Flag (CTF) challenge during a competition that led me down a rabbit hole of cybersecurity exploration. Let me take you through my journey of discovering and exploiting a vulnerable libssh service, unraveling the mystery step by step.

It all began with a simple IP address and port number. Armed with my trusty Kali Linux machine, I decided to probe the service using the netcat utility. Connecting to the IP with the specified port, I soon discovered that it was a libssh service.

How did I know? The connection confirmed it, and I was ready to dive deeper into this intriguing puzzle.
Unveiling Vulnerabilities:
With the service identified, my next task was to pinpoint potential vulnerabilities. A quick search revealed the version details of the libssh service in use. Armed with this information, I navigated to the project’s GitHub page and stumbled upon an exploit script written in Python. It was a eureka moment — the service was indeed vulnerable!

The Exploitation:
Copying the exploit script to my Kali machine, I made a few modifications to tailor it to the specific IP and port.
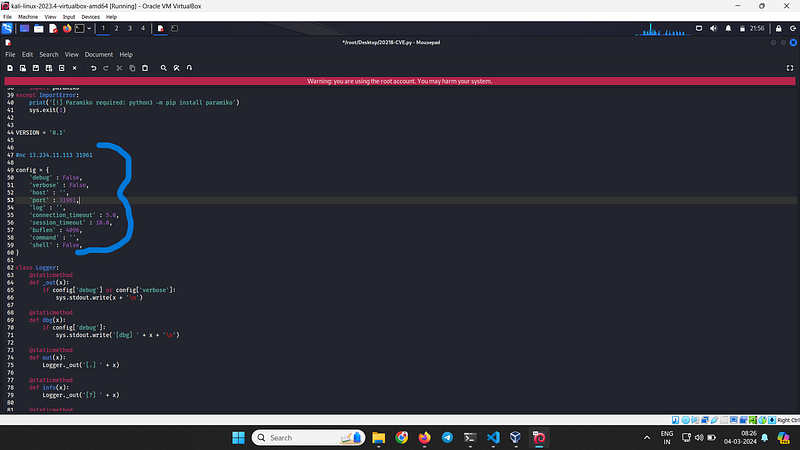
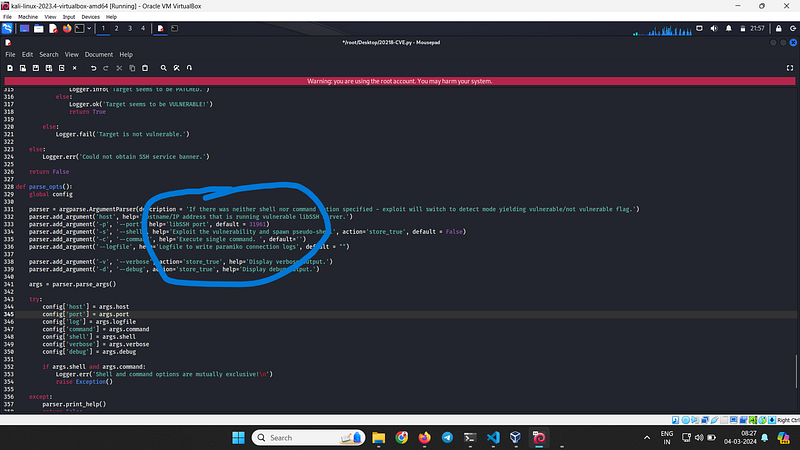
After saving the edited script, I launched it with bated breath. Running a simple command ‘uname -a’ confirmed my suspicions — the port was indeed vulnerable.

It is vulnerable and now we can easily exploit.

here we got directory access


With adrenaline coursing through my veins, I executed the exploit script. Within moments, I gained access to the root directory of the server, a significant breakthrough in the CTF challenge. The feeling of accomplishment was palpable as I navigated through the server’s files, unraveling its secrets one by one.
Conclusion:
My journey into the depths of cybersecurity had led me to uncover vulnerabilities in a libssh service, demonstrating the importance of thorough penetration testing and the critical role it plays in securing systems against potential threats. As I reflect on this experience, I am reminded of the endless possibilities and challenges that await those who dare to venture into the realm of ethical hacking and cybersecurity.
By Sachin kewat on .
Comments
Post a Comment